Computers & Technology
epub |eng | 2016-08-19 | Author:Unknown
The Fighting on 22 April The tasks of the armies of the front’s main shock group for 22 April remained as before. In order to secure the right flank of ...
( Category:
Photography & Video
March 26,2020 )
epub |eng | 2013-11-27 | Author:Muhammad Ali Babar & Alan W. Brown & Ivan Mistrik
7.9 Conclusion Architecture analysis is a broad topic, which is addressed by a large number of different analysis methods and techniques. Available analysis approaches differ considerably in various aspects, including ...
( Category:
Software Development
March 26,2020 )
epub |eng | | Author:Unknown
Policy-Based Consensus Data Aggregation for the Internet of Things Firas Al-Doghman1 , Zenon Chaczko1 and Alina Rakhi Ajayan1 (1)Faculty of Engineering and IT, University of Technology Sydney, Sydney, Australia Firas ...
( Category:
Architecture
March 26,2020 )
epub |eng | 2020-03-19 | Author:Vanamala, Srinivas [Vanamala, Srinivas]
Live Preview Exercise 2 Download the Exercise 2 Exercise 2: Add the “!!!’ before every paragraph Tip: use p::before to apply the rule before the paragraph. Live Preview 3 CSS ...
( Category:
Programming
March 26,2020 )
epub |eng | | Author:Aboul Ella Hassanien & Diego Alberto Oliva
4 Methodology Methodology consists of two phases called watermarking and authentication. For watermarking, the FHT mechanism is used which is discussed in Sect. 4.1 in detail. For authentication, the SVD ...
( Category:
Computer Science
March 26,2020 )
Audio Source Separation and Speech Enhancement by Sharon Gannot & Tuomas Virtanen & Emmanuel Vincent
epub |eng | 2018-10-21 | Author:Sharon Gannot & Tuomas Virtanen & Emmanuel Vincent [Sharon Gannot]
( Category:
Networking & Cloud Computing
March 26,2020 )
epub |eng | | Author:Unknown
Palaeo-Eskimo Land Use Ongoing research in the interior of southern Baffin Island has resulted in the identification of many previously unknown Palaeo-Eskimo occupations. These sites are variously located on the ...
( Category:
Architecture
March 26,2020 )
epub |eng | | Author:Bing-Yuan Cao & Ji-Hui Yang & Xue-Gang Zhou & Zeinab Kheiri & Faezeh Zahmatkesh & Xiao-Peng Yang
5.2.2 Solving Solution on Model (5.2.2) Let us consider the function as follows. (5.2.6) the taken optimum value of f(x) is related to exponent of . Now we discuss Model ...
( Category:
Processes & Infrastructure
March 26,2020 )
epub, pdf |eng | 2013-07-11 | Author:Unknown
NOTES 1 Degrees (and even types) of risks will vary greatly for the procurement of different organs and tissue and among prospective donors. This fact does not affect our argument ...
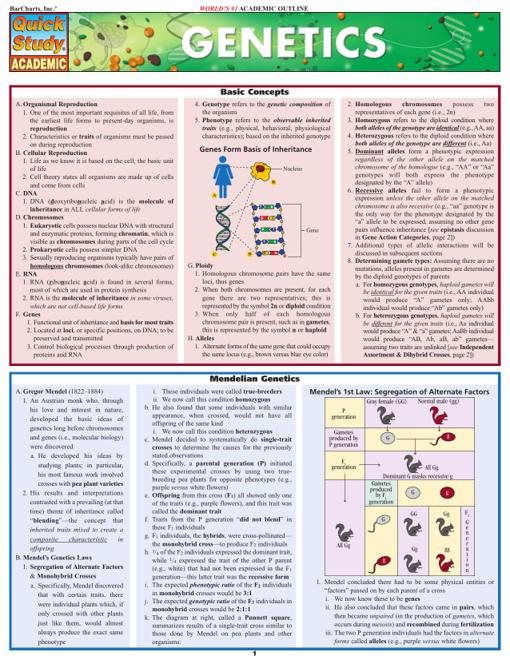
( Category:
Genetics
March 26,2020 )
epub, pdf |eng | 2019-01-22 | Author:Frances Buontempo [Frances Buontempo]
( Category:
Business Technology
March 26,2020 )
epub |eng | 2020-01-29 | Author:Danesh Kuruppu & Kasun Indrasiri [Danesh Kuruppu]
Example 5-5. gRPC deadlines for the client application conn, err := grpc.Dial(address, grpc.WithInsecure()) if err != nil { log.Fatalf("did not connect: %v", err) } defer conn.Close() client := pb.NewOrderManagementClient(conn) clientDeadline ...
( Category:
Design & Architecture
March 26,2020 )
epub |eng | 2020-03-24 | Author:Matthias Broecheler & Denise Gosnell [Matthias Broecheler]
( Category:
Intelligence & Semantics
March 26,2020 )
epub, pdf |eng | | Author:Antti Laaksonen
Since we know that a node always has less than n ancestors, it suffices to calculate values for each node and the preprocessing takes time. After this, any value of ...
( Category:
Algorithms
March 26,2020 )
epub |eng | 2017-02-01 | Author:Johny Beltran [Beltran, Johny]
( Category:
Marketing & Sales
March 26,2020 )
epub |eng | | Author:Ben Rady
Joe asks: But You Promised?! Given my preference for web standards, you might be wondering why we’re not using a Promise/A+ compatible object to manage our identity information. Since Promises ...
( Category:
Software Development
March 26,2020 )
Categories
Popular ebooks
Deep Learning with Python by François Chollet(27922)The Mikado Method by Ola Ellnestam Daniel Brolund(25230)
Hello! Python by Anthony Briggs(24263)
Secrets of the JavaScript Ninja by John Resig Bear Bibeault(23352)
Kotlin in Action by Dmitry Jemerov(22437)
The Well-Grounded Java Developer by Benjamin J. Evans Martijn Verburg(21903)
Dependency Injection in .NET by Mark Seemann(21786)
OCA Java SE 8 Programmer I Certification Guide by Mala Gupta(20648)
Algorithms of the Intelligent Web by Haralambos Marmanis;Dmitry Babenko(19477)
Grails in Action by Glen Smith Peter Ledbrook(18553)
Adobe Camera Raw For Digital Photographers Only by Rob Sheppard(17020)
Sass and Compass in Action by Wynn Netherland Nathan Weizenbaum Chris Eppstein Brandon Mathis(15810)
Secrets of the JavaScript Ninja by John Resig & Bear Bibeault(13660)
Test-Driven iOS Development with Swift 4 by Dominik Hauser(11807)
Jquery UI in Action : Master the concepts Of Jquery UI: A Step By Step Approach by ANMOL GOYAL(11133)
A Developer's Guide to Building Resilient Cloud Applications with Azure by Hamida Rebai Trabelsi(10618)
Hit Refresh by Satya Nadella(9175)
The Kubernetes Operator Framework Book by Michael Dame(8559)
Exploring Deepfakes by Bryan Lyon and Matt Tora(8396)
Robo-Advisor with Python by Aki Ranin(8340)